views
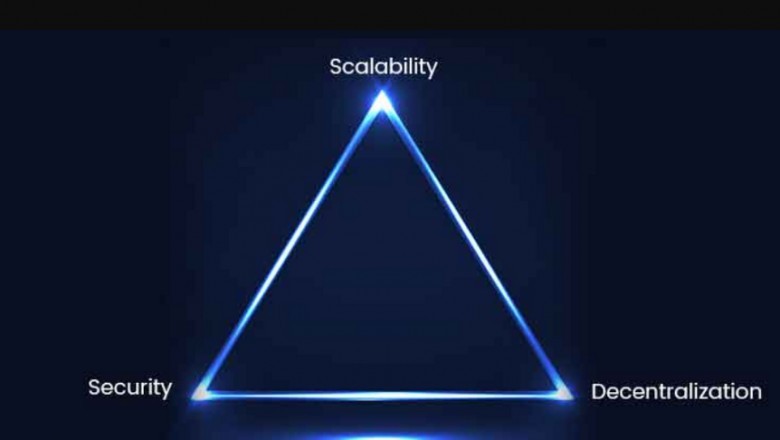
The Bitcoin scalability trilemma was invented by Ethereum founder Vitalik Buterin. The trilemma describesThe commitments that the creators of cryptocurrency projects must make to optimize the structure of the blockchain.
Simply put, you can’t do it all at once. The trilemma has three elements: decentralization, security, and scalability. The article briefly describes the three elements, their advantages and disadvantages. The trilemma allows you to compare Blockchain Development against each other. In general, the problem is not weak infrastructure, although this happens, but what aspects of the blockchain the project seeks to optimize and if they correspond to the proposed value and purpose of use. This is an educational article — it will help readers independently evaluate cryptocurrencies.
Decentralization
- Decentralization is the degree of distribution of rights, ownership, influence, and value on the blockchain. The degree of decentralization is important as it is not a binary component. Ethereum has a high degree of decentralization, Eos has a partial degree of decentralization, and Twitter has no decentralization. Many people mistakenly believe that networks are decentralized or centralized, or that all blockchains are decentralized in the same way.
- Let’s start with the most centralized organizations. They generally don’t use blockchain. In them, control is exercised by a small group of people: the management, who often owns a large part of the company. Management consists of decision makers and an advisory board. Today, most companies work with this principle.
- In decentralized networks, the main control is in the hands of the users who, thanks to their actions, can vote, use the services of the platform and make a profit. In all blockchains, users buy tokens to vote, but are given different powers of influence for this, depending on the structure of the network. In protocols with proof of ownership, the strength of the user’s voice depends on the number of tokens he owns. In protocols with delegated proof of ownership, participants use actions to select a third party to vote on their behalf. However, most of this management structure is written in your code, so voting is usually carried out to resolve disputes. In other systems, decisions about changing strategy,
- Decentralized blockchain developement has another important property: in it, most of the value belongs to the participants. There is no “leadership”: a centralized body that first takes its share and distributes the rest to the rest of the participants. Most cryptocurrency projects do not belong to the founders, but to participants or users. Such a system is beneficial to everyone except the founders. Let’s take a look at the music industry: Apple (iTunes) charges 30% of sales for hosting and distribution, with the remaining 70% going to musicians. If the music industry worked on the blockchain, musicians would receive more than 90% of the value. Other participants who provide the network would also receive a small amount, but most of the value would be transferred to its creators,
- Advantages and disadvantages of decentralized protocols:
- In terms of philosophy, decentralization returns power to society. The management rules in blockchain are written in code and cannot be changed, therefore, the network provides the maximum distribution of power, wealth and tenure rights.
- Generally, the more decentralized the system, the more reliable it is: it does not have a central point of failure vulnerable to hacking. However, even the most decentralized system can be hacked.
- In decentralized protocols like Bitcoin and Ethereum, miners create new blocks using the PoW protocol — they solve complex problems to find a hash. It takes a lot of power, performance and speed are reduced, negatively affecting the efficiency of blockchains that require high bandwidth.
- On blockchains, where disputes are resolved by all members of the community, there are no central moderators. On social media, its absence leads to the appearance of a hat and fake news.
- A decentralized blockchain is difficult to shut down as it does not have a centralized server or authority. On the one hand, this is an advantage, but if the blockchain starts to cause damage and its participants cannot solve the problem, the decentralized nature of the network will complicate the process of removing the blockchain.
Security is the level of protection of the blockchain against external attacks, and from the point of view of the internal system of the blockchain, the degree of its immutability. Most blockchains are significantly susceptible to security risks. There is a connection between decentralization and security. Often times, the more nodes on the network, the less it depends on the central authority, which means there is less risk of breaking a single point of failure. However, there are other types of attacks that threaten decentralized networks:
- A> 50% attack occurs when one participant (or multiple participants) receives more than 50% of all tokens and takes control of the entire network.
- Sibyl Attack — Member (or more) participants) create many (hundreds, thousands and more) identifiers in the system to gain control of a large part of the property and / or make decisions on the network.
- Spam attack: one participant (or several participants) fills a network with transactions with low amounts to stop the blockchain.
- A DDoS attack (distributed denial of service attack) occurs when an attacker disrupts network traffic and floods it with malicious transactions.
- Collusion attack: One or more participants (or nodes) agree to perform malicious activities on the network.
- The main advantage of high security is blockchain protection against attacks. This is especially true for systems that require maximum security and work with sensitive data. A high level of security is needed throughout the financial services industry. A blockchain would even protect cryptocurrency exchanges, one of the main targets of hackers. (We are talking about new decentralized cryptocurrency exchanges here, one of the promising ideas of a decentralized app on Eos.)
- A high level of security has no drawbacks, but it does create several side effects. Many secure blockchains use PoW protocols, in which miners need to solve complex hash search tasks to create blocks. These protocols consume a large amount of processing power and energy, reducing bandwidth and increasing network latency. This repels many potential users who are used to almost instantaneous transactions on centralized networks. Platforms with a focus on security can compromise so much, but if the main task is to optimize the user experience, then the security issue needs to be reconsidered.
Scalability is an important component of network bandwidth. In other words, it sets an upper limit on the potential size of the network. The maximum number of users is a critical aspect of network evaluation. Today, the Bitcoin network has 2.9–5.8 million wallets; Facebook has 4 billion users, Eos has several thousand. One of the most scalable platforms is Nano. Advantages of Nano: 1) the network compresses transactions into small UDP packets (similar to zip files), so most standard computers can process transactions; 2) each user provides power for their own transactions on their own blockchain; there is no single large blockchain on the network that other users must support;
To provide infinite scalability, you have to sacrifice something. In a scalable and decentralized network, a high security risk. Developers choose the most suitable platform for their needs, and users choose the most productive. Some are willing to sacrifice security for scalability; others are willing to sacrifice scalability for security. We evaluate the basic functions of the system based on its general structure.
The benefits
- Scalability ensures fast application operation and the ability to process a large volume of transactions, which is especially true for sites with streaming audio / video, games, and social media.
- When the application uses more users than expected, a scaled network can bear the load. For example, the Cryptokitties network on Ethereum did not have great scalability, which is why it encountered serious problems.
- The main disadvantage of infinite scalability- Low security. Almost all of the above security threats are increasing on a large-scale network. Active growing networks must have a rapid consensus mechanism to commit more transactions and process user requests at the same speed. This is only possible on blockchains with proof of ownership or with delegated proof of ownership. But in such a network, decentralization is reduced. In protocols with proof of work, it will be necessary to simplify the search for hashing or mining algorithms to ensure fast processing of transactions. This undermines security and to some extent decentralization (mining pools will benefit if the tasks of finding a hash become easier).
- Buterin was right: it is difficult to create a Blockchain Development Company platform with three equally developed aspects. Users and developers must select and optimize a maximum of two of the three components. In the end, everyone decides what to wear based on project goals and personal preferences.