views
Vulnerability assessment and patch management are two key features that most Mobile Device Management solutions lack. TAC Security can provide automatic onboarding and regular scanning of your mobile devices through integration with a popular MDM like Microsoft Intune, among other features, to give a complete security posture for mobile devices.
Whether in bank branches, industrial plants, or retail outlets, mobile devices play a critical part in today's corporate processes. Business apps and data are increasingly held on phones and tablets, which are subject to regulatory compliance and security. Securing mobile devices has become more complex as the security risk for mobile devices has grown.
Pegasus malware has been used in more data breach attacks recently, and Apple has released an urgent release five times this year to resolve serious zero-day vulnerabilities. Only if the gadget is vulnerable may such security flaws occur. Android and iOS vulnerabilities have risen dramatically, with a considerable increase in vulnerabilities that can lead to data leaks. Code execution, Overflow, Gain Information, and DoS are all methods that attackers can use to gain control of mobile devices on Android and iOS.
The Limitations of MDM and EMM Solutions
Mobile Device Management (MDM) and Enterprise Mobility Management (EMM) solutions don't give you significant visibility into these flaws, and they don't assist you patch them.
EMM solely meets the needs of the IT team, not the Security team, and the Security team is not permitted to use these solutions to generate security and audit reports. MDM solutions do not provide visibility into common vulnerabilities, nor do they provide a complete picture of a device's security posture. Devices in an enterprise are more vulnerable to data breach assaults due to a lack of awareness into vulnerabilities and no patch management.
Enterprises require a mobile security solution that protects all mobile devices, monitors them in real time, and gives them visibility into their security posture. The onboarding process is one of the most difficult aspects of most mobile security systems because it relies on end-user intervention. Another issue is automation. Once onboarded, automated vulnerability assessments should be performed on a regular basis. Mobile security should be able to exchange vulnerability info with the SIEM system in order to schedule corrective actions.
Even though most MDMs lack these features, Tac Security has begun the process of integrating with some of the most popular ones, starting with Microsoft Intune.
Microsoft Intune's Automated Vulnerability Assessment
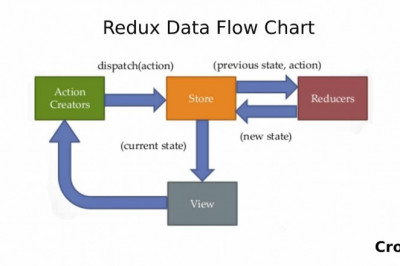
Automated onboarding and vulnerability assessment are key capabilities that should be included in every mobile security solution. Through its interface with Microsoft Intune, TAC Security VMDR for mobile devices automates the onboarding process. VMDR can now scan your Intune MDM-enrolled devices without the need to install the TAC Security Cloud Agent and without the need for end-user participation.
Without the need for user intervention, once a device is onboarded, it undergoes a persistent vulnerability review based on the most recent synced data. You may sync TAC Security vulnerability detection data with your internal SIEM to configure remediation activities using TAC Security APIs. You can also perform virtual actions on devices instantly from the TAC Security interface.
Configure Connectors to Discover Vulnerable Devices
You must first configure the connectors before you can sync your enrolled devices from Microsoft Intune with TAC Security VMDR for mobile devices. Initially, you may only use the connector to sync devices that are enrolled in Intune EMM.
The configuration of the connector is a each task. For more setup information, see the Secure Enterprise Mobility User Guide. You'll see the Intune enrolled devices in TAC Security, as well as the vulnerability assessment result, once the connector is configured and synced successfully. A vulnerability scan will also be performed on every connector sync.
TAC Security Global Asset Inventory receives the assets synced from Intune. In the event that any devices get significantly compromised, you can conduct actions such as Send Messaged and Factory Reset remotely.
All customers with a VMDR for mobile devices subscription now have access to TAC Security Integration. To get this functionality enabled for your membership today, contact your Technical Account Manager (TAM) or Support.